GraphQL in Enterprise - Are you Ready?
Overview
CIOs and technology leaders are now likely aware of the growing popularity of GraphQL, the open source API query language. Like how Kubernetes adoption unfolded within organizations over the past few years, developers are largely leading the internal charge—championing GraphQL as a modernized replacement for legacy REST APIs.
According to Gartner, more than half of enterprises will be using GraphQL in production by 2025; in 2021, fewer than 10% were. This rapid shift is driven in part by the need to expose API data and functionality to third-party developers, which has become increasingly popular. GraphQL is a far more flexible, scalable, and easier-to-use option than REST. It’s become the cornerstone of widespread API modernization initiatives, and it is vastly more efficient and effective to use for developers.
However, with over 50% of APIs being “unmanaged”—and with enterprises producing and consuming an exponentially growing number of APIs—come new security risks.
What is an “unmanaged” API? Unmanaged APIs are APIs that have been created by a developer but are not discovered by the people who manage the GraphQL schema (i.e., the engineers/architects/CIO teams who are responsible for making sure that API development is efficient and secure, and that the schema itself is always optimized).
These unmanaged APIs are commonly referred to as “shadow APIs.” Going undiscovered and/or invisible, shadow APIs also prevent enterprise architects from optimizing schema planning and business logic across the organization. They then cannot enforce standards across subgraphs and manage resource consumption, resulting in Service Level degradation (latency) as well as inefficient and costly development.
Furthermore, both shadow APIs and unsecured APIs pose an ongoing threat to the enterprise. The compliance and security teams lack the ability to enforce access control, detect anomalies, and secure the code, opening the organization to threats of unauthorized data access and breaches, as well as heavy financial and reputation losses.
This raises the question: why are existing application gateways not sufficient to help with the transition to GraphQL? Most API and web application gateways that enterprises have in place cannot discover GraphQL traffic and cannot provide the depth and context necessary to deliver visibility, discoverability, or real-time protection. Because GraphQL operations are sent as a single request, it’s difficult to understand how that request is being handled and what services are being called; all GraphQL traffic is seen at a high level, without details or granularity. Inigo was created to specifically address these gaps in API management, governance, and security for GraphQL APIs. Our solution goes into depth for each query, and with our innovative intellectual property, it not only makes GraphQL APIs visible and manageable but also provides real-time protection, Importantly, it delivers these capabilities regardless of the measures put in place by the developer, enabling CIOs and platform teams to move into API modernization with GraphQL with confidence.
Inigo’s GraphQL gateway provides schema-based access control, so your team can define and enforce access policies based on the schema of your GraphQL APIs, rather than the underlying code. Doing so ensures that only authorized users and applications can access the data and functionality exposed by the APIs.
Second, Inigo delivers compliance with a full audit trail and PII detection. This allows your enterprise to track and monitor all of the interactions related to your GraphQL APIs, and to detect and prevent the leakage of sensitive personal information.
Third, Inigo provides protection from spec abuse, injections, and object-level rate limiting. This helps organizations prevent and mitigate different types of attacks, such as query overloads, data breaches, and service disruptions.
In addition to security, Inigo’s platform enhances the developer experience and adds key workflow efficiencies, including:
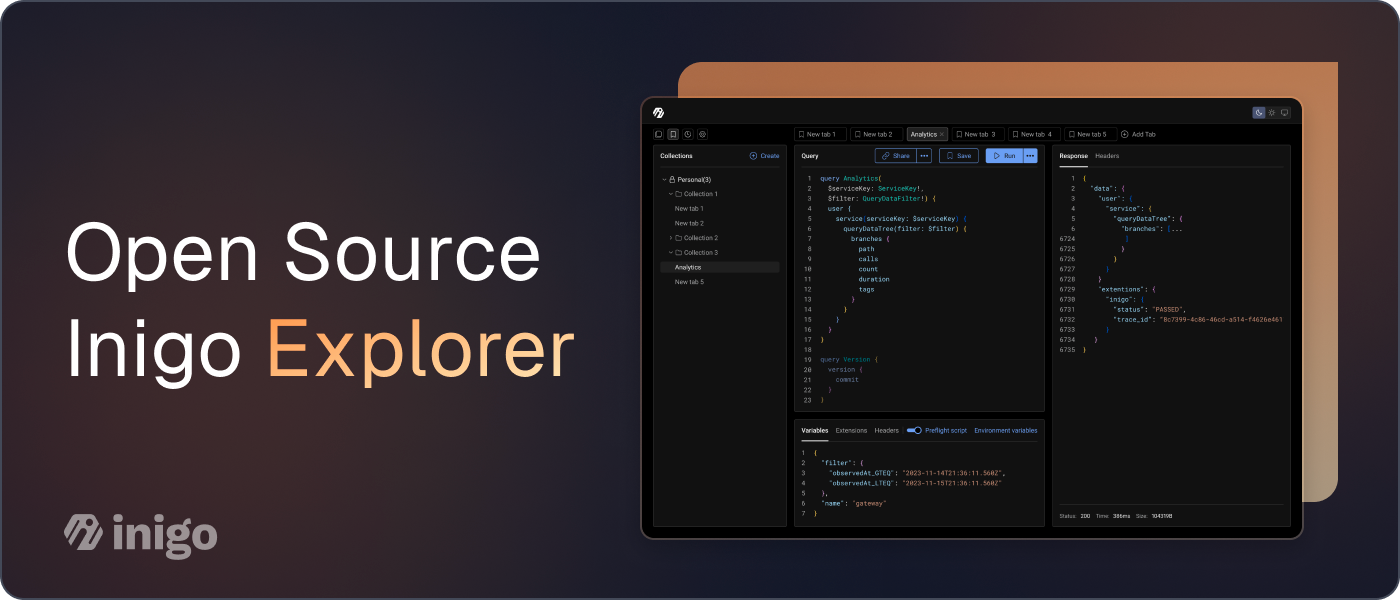
- Operations and performance optimization, which allows developers to monitor and improve the performance of their GraphQL APIs in real time.
- API lifecycle management with CI tools, which helps developers automate the deployment and testing of their GraphQL APIs.
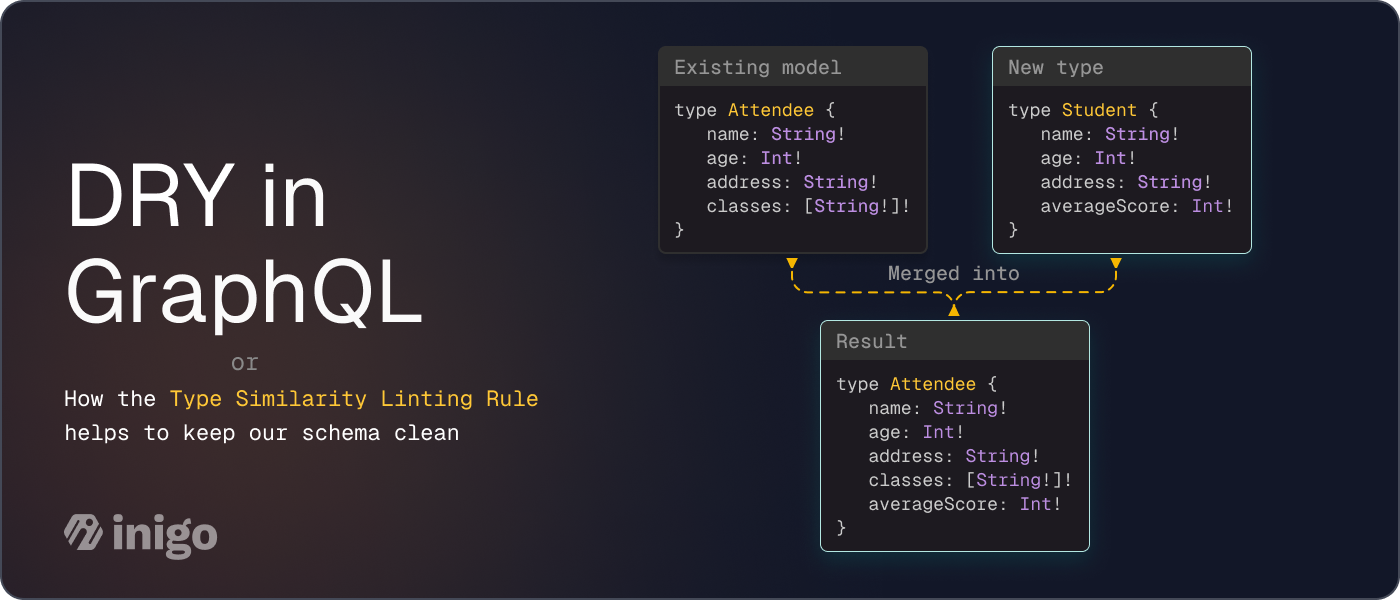
- Schema planning, which enables developers to design and implement GraphQL APIs in a modular and extensible way.
- Granular query sub-graph analytics, which gives developers insights into the usage and behavior of their GraphQL APIs, and helps them to optimize and evolve them over time.
Inigo offers a more affordable solution compared to other data and analytics tools. It delivers GraphQL-specific capabilities that other tools are too expensive to apply to GraphQL deployments. Additionally, Inigo is SOC-2 compliant—which means that it meets the strict security and compliance standards required by many organizations.
If you want to experience our solution, or see a demo, reach out to us at [email protected]