The Ultimate Guide to GraphQL Security: Protecting Your APIs from Emerging Threats

Like any new technology, security awareness often lags behind adoption. As a result, GraphQL vulnerabilities are increasingly becoming a target for attackers. From GraphQL injection to data leaks, the attack surface is vast and unique. Unlike traditional REST APIs, a single GraphQL query can expose multiple data sources in a single request, making security testing essential for any deployment.
This guide will explore the key GraphQL security issues, how they impact organizations, and the strategies to secure your GraphQL implementation.
Understanding GraphQL Security Awareness
To gauge how security-conscious GraphQL users are, we conducted a Reddit survey titled "How Do You Think About GraphQL Security?" The results were both interesting and concerning:
Through one-on-one interviews, we discovered that those aware of GraphQL’s attack surfaces typically learned about them the hard way—after experiencing a security breach firsthand.
Common GraphQL Security Issues & Attack Surfaces
GraphQL APIs introduce new security challenges that are often overlooked by traditional security measures. Attackers can exploit multiple vulnerabilities, including:
- Parser Attacks – Exploiting weak parsing logic to crash GraphQL services.
- Resolver Attacks – Targeting poorly written resolvers to manipulate data.
- Data Leaks – Unauthorized access to sensitive information through improper schema exposure.
- GraphQL Injection – Injecting malicious payloads to compromise underlying databases.
Who Is Impacted?
Short answer: most GraphQL users.
GraphQL is available in multiple programming languages, but not all implementations offer the same level of security. Recently, a circular-fragment attack was demonstrated on Aago’s Ruby-based server, leading to a CVE security disclosure.
Security researchers like Nick Aleks have documented vulnerabilities across multiple GraphQL implementations:
Engineering teams with significant resources often build custom GraphQL security tooling, but this approach is difficult to maintain and prone to errors. Platforms like HackerOne have reported several real-world GraphQL attacks, emphasizing the need for proactive security measures.
How to Secure Your GraphQL APIs
Implement GraphQL Security Testing Regular GraphQL security testing helps identify GraphQL vulnerabilities before attackers do. Automated penetration testing tools can simulate common attack patterns, such as:
- Excessive nested queries leading to Denial of Service (DoS).
- Exploiting introspection queries to expose sensitive schema information.
- Crafting malicious GraphQL injection payloads.
Protect Against Denial-of-Service (DoS) Attacks GraphQL’s flexible nature makes it vulnerable to DoS attacks. Attackers can send deeply nested queries that overwhelm backend systems. To mitigate this risk:
- Field-Level Rate Limiting – Restrict access to expensive queries.
- Cost-Based Rate Limiting – Evaluate and block high-complexity queries.
- Operation Registry – Allow only pre-approved queries to run.
Secure Introspection & Access Controls GraphQL introspection is a double-edged sword—it helps developers understand schemas but also exposes API structure to attackers. Use RBAC introspection separation to enforce access control and restrict schema visibility media based on user roles.
Enforce Query Limits & Prevent Data Scraping Since GraphQL allows clients to request arbitrary data structures, attackers can abuse this feature for data scraping. Protect your API by:
- Setting query depth and complexity limits.
- Monitoring API traffic for unusual patterns.
- Preventing GraphQL injection attacks with strict input validation.
Leverage Platform-Agnostic GraphQL Security Solutions Standard API gateways cannot detect GraphQL-specific threats. That’s where solutions like Inigo come in—providing advanced security for GraphQL environments. Get started in less than 15 minutes to see how Inigo can protect your GraphQL infrastructure.
Related GraphQL Security Resources
To deepen your knowledge of GraphQL security and performance optimization, check out these related guides:
- GraphQL vs. REST: Key Differences
- Optimizing GraphQL Performance
- Handling GraphQL Responses & Error Handling
- GraphQL Use Cases & Real-World Applications
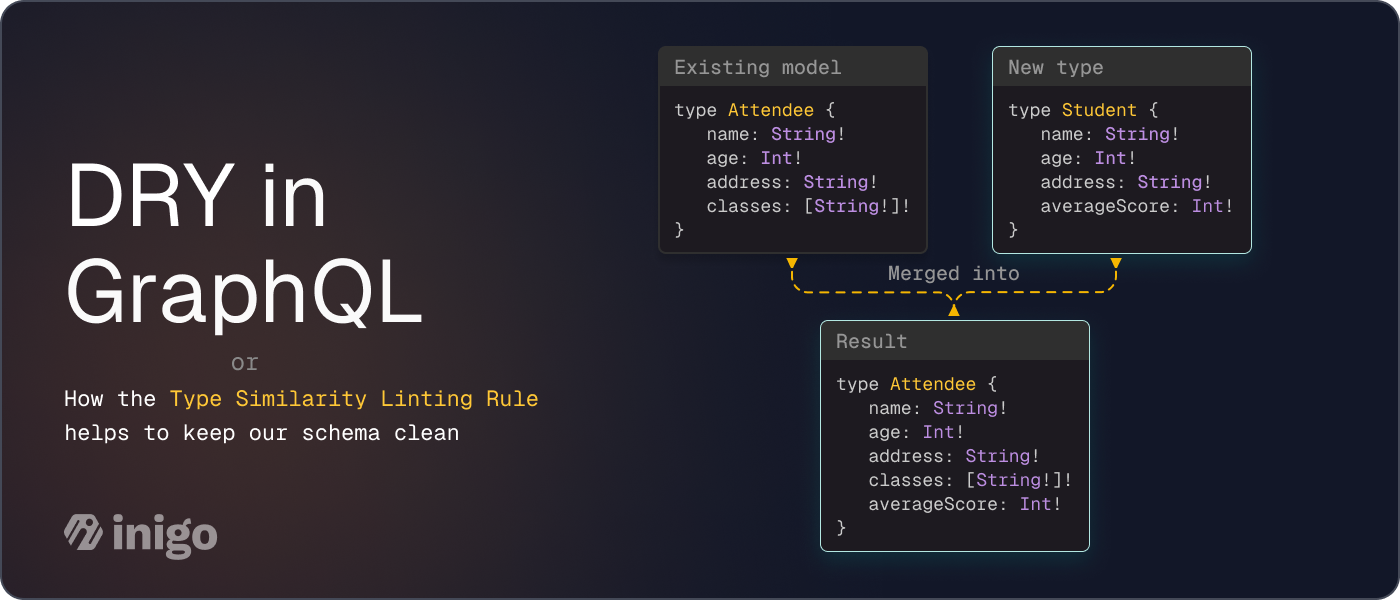
- Best Practices for GraphQL Schema Design
- Apollo Client: Breaking Free from Vendor Lock-in
Final Thoughts
Securing GraphQL APIs is no longer optional—it’s a necessity. The growing number of GraphQL security vulnerabilities makes it crucial for developers to integrate security best practices from day one. By implementing GraphQL security testing, enforcing query rate limits, and using platform-agnostic security solutions, you can stay ahead of attackers.
Ready to defend against GraphQL server vulnerabilities? Inigo can help! Schedule a demo now.